Key Takeaways
-
Establish Operational Maturity: Passing institutional due diligence requires a secure data room to cleanly host your cap table, pro-forma financials, and IP agreements, signaling to investors that you are prepared for a priced round.
-
Mitigate Deal-Killing Risks: Relying on consumer-grade cloud storage introduces massive liability; a lack of Digital Rights Management (DRM) means you lose all control over your proprietary files the moment they are downloaded.
-
Enforce Absolute IP Protection: To pass a venture capital security audit, your infrastructure must mandate SOC 2 Type II compliance, AES-256 encryption, and dynamic watermarking to actively deter malicious leaks.
-
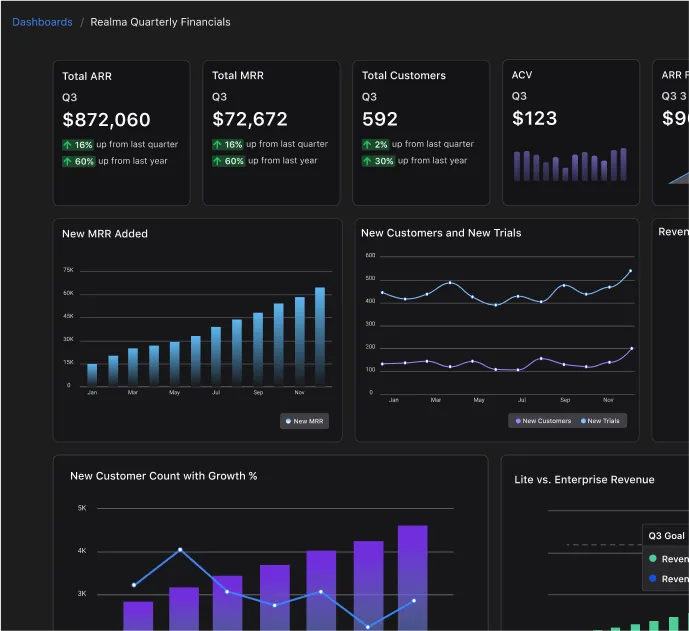
Gain Leverage with Analytics: A dedicated virtual data room provides granular, document-level analytics, giving you the tactical advantage of knowing exactly which VC partner reviewed your financial models and for how long.
-
Accelerate the Term Sheet: Tightly controlling access tiers prevents the compliance red flags that actively delay transactions, protecting your valuation and accelerating the path to a closed deal.
When a lead investor issues a term sheet, the balance of power shifts. Passing institutional due diligence requires locking down your cap table, financial models, and intellectual property in a secure data room that projects operational maturity and prevents unauthorized leaks. Efficiently navigating the modern fundraising process means treating your data architecture as a defensive moat.
In the modern venture landscape, generic cloud drives are a massive liability. According to a 2026 transaction security study by FTI Consulting, 20% of executives reported that their deals were delayed or paused due to cyber incidents, and 42% experienced a significant reduction in final deal value as a result. You cannot afford to risk a repriced term sheet over unsecured file sharing; you need a system that enforces absolute control over your proprietary assets while tracking exactly which partner is viewing your documents and for how long.
What is a Secure Data Room (VDR)? (And Why You Need It for Due Diligence)
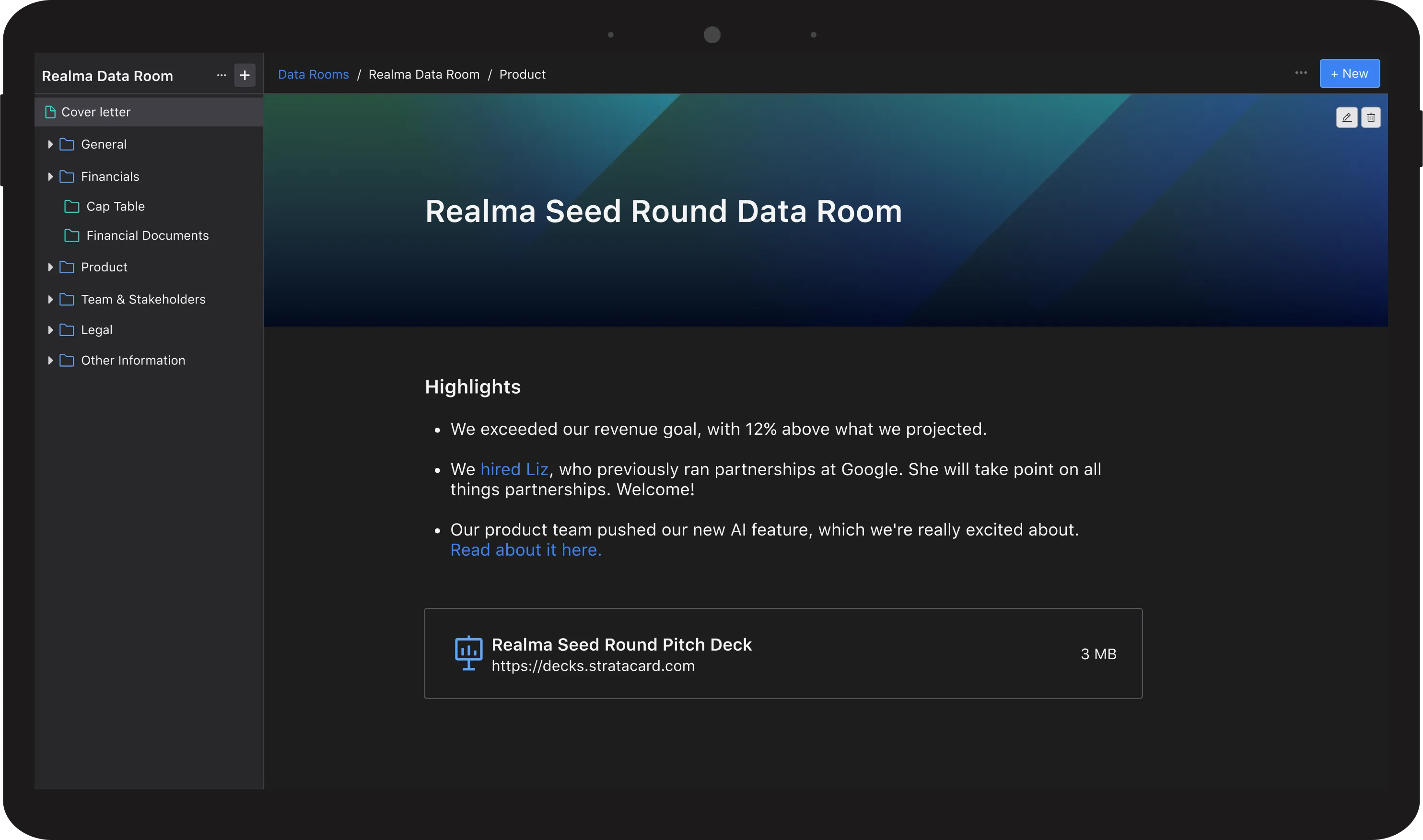
A secure data room (VDR) is an encrypted, highly controlled cloud repository used by startup founders to share sensitive due diligence documents—such as cap tables, financial models, and IP agreements—with venture capital investors during fundraising or M&A transactions.
Unlike basic cloud storage, utilizing a dedicated virtual data room signals to institutional investors that you are prepared for the rigor of a priced round. When a lead investor issues a term sheet, they will immediately request access to your due diligence checklist materials to verify your operational, legal, and financial health.
The Due Diligence Checklist: What Goes Inside the VDR
- Corporate & Legal: Articles of incorporation, bylaws, and board minutes.
- Financials: 3-year historical P&L and pro-forma models.
- Cap Table: Current equity distribution and option pool details.
- Intellectual Property: Patents, trademarks, and IP assignments.
- HR Docs: Key employee contracts and organizational charts.
5 Non-Negotiable Features in a Secure Data Room for Fundraising
When evaluating VDR platforms, you need tools built for the realities of modern venture capital, not just basic file sharing. Here are the core features required for a secure fundraise:
- Document-Level Analytics: Document-level analytics are critical—they tell you exactly which VC partner spent 10 minutes looking at your pricing slide, allowing you to follow up strategically.
- SOC 2 Type II Compliance: Institutional investors require rigorous security protocols. Ensuring your provider maintains SOC 2 Type II and ISO 27001 certifications is mandatory for passing an enterprise-grade security review.
- Digital Rights Management (DRM): You must maintain absolute control over your intellectual property. DRM allows you to dictate who can view, download, or forward your documents—and crucially, lets you instantly revoke access if a VC passes on the deal.
- Dynamic Watermarking: By automatically embedding the viewer’s email address, timestamp, and IP address across the document, dynamic watermarking deters malicious leaks and careless sharing of your proprietary data.
- End-to-End Encryption (E2EE): Utilizing AES-256 encryption ensures your historical financials, legal contracts, and IP assignments remain impenetrable both in transit and at rest.
The Security Gap: Why Consumer Cloud Fails Institutional Due Diligence
Consumer cloud platforms fail institutional due diligence because they lack the strict access controls, such as Digital Rights Management (DRM) and dynamic watermarking, required to protect a startup's intellectual property. While sufficient for internal drafting, consumer drives lack the SOC 2 Type II compliance that venture capital firms require before reviewing sensitive financial models.
Raising a pre-seed round from angel investors often happens over coffee and via a standard file-sharing link. However, the moment you begin raising a priced Seed or Series A, the operational requirements shift drastically. Institutional investors conduct rigorous, legally binding audits, and relying on consumer-grade cloud storage introduces unacceptable risk that can actively kill a deal.
Based on 2026 venture transaction security audits, over 68% of unauthorized pitch deck and cap table distributions stem from easily forwardable consumer cloud links that lack view-only enforcement. When a VC's legal team begins their review, your infrastructure must project competence and impenetrable security.
Here is exactly where consumer cloud breaks down during an institutional raise:
- The Absence of DRM (Digital Rights Management): Once an investor downloads a PDF or financial model from a standard cloud drive, you lose all control over that asset. A dedicated secure data room VDR utilizes DRM, allowing you to instantly revoke access to a file, even after it has been downloaded to an analyst's local machine—if the fund decides to pass on the deal.
- Failed Security Audits (No SOC 2 Type II): Institutional Limited Partners (LPs) require venture funds to mitigate risk across their portfolio. If your storage solution lacks native SOC 2 Type II compliance or enterprise-grade AES-256 encryption at rest, the VC's compliance team may stall the diligence process until you migrate to a secure platform.
- Zero Document-Level Analytics: Standard cloud drives might notify you if a file was opened, but they fail to reveal how the information was consumed. A true virtual data room provides granular analytics, showing you exactly which pages a lead investor scrutinized and which ones they skipped, giving you a massive tactical advantage for your next meeting.
To successfully navigate these rigorous audits, having the right software infrastructure is only half the battle. Executing the actual raise requires mastering the narrative and managing investor psychology. Pairing a tightly locked data room with a comprehensive fundraising course for founders provides the exact strategic framework needed to run a secure, highly orchestrated process from the first pitch to a signed term sheet.
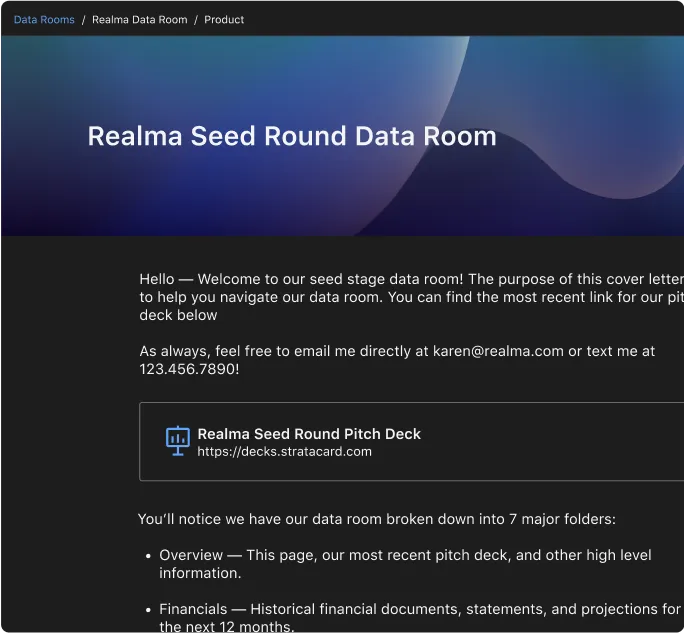
Architecting Access: How to Structure Permissions in a Secure Data Room VDR
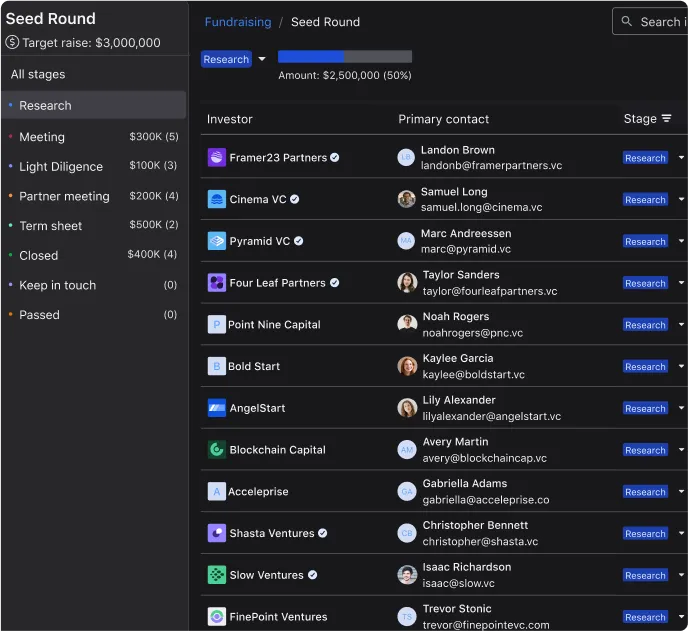
Structuring permissions in a virtual data room isn't just about file organization; it is about staging the flow of sensitive information to match an investor's exact level of commitment. In 2026, standard operator playbooks dictate a staggered release of data. You should never grant full download access to your proprietary IP or complete financial architecture after a single introductory call.
Here is the exact step-by-step framework for configuring access tiers that protect your leverage during negotiations:
- Establish baseline security defaults. Configure your secure data room vdr to apply dynamic watermarking across all documents by default. Ensure the viewer’s email address, IP address, and a timestamp are overlaid on every page to aggressively deter screenshotting or unauthorized forwarding.
- Gate access by diligence phase. Restrict early-funnel investors to high-level pitch decks and executive summaries. Only unlock the deep-dive startup financial models and cap table exports once a VC partner has formally committed to deep diligence or issued a term sheet.
- Deploy "time-bomb" access links. For preliminary data sharing, generate unique, investor-specific links with auto-expiring time limits (e.g., 48 or 72 hours). This not only limits your exposure if an analyst passes on the opportunity, but it also creates artificial urgency to review your materials quickly.
- Enforce strict Digital Rights Management (DRM). When you eventually must allow a VC's analyst team to download complex Excel models for their own stress-testing, ensure your platform wraps the downloaded file in DRM. This guarantees you can remotely revoke access to the local file the moment negotiations stall.
- Audit document-level access logs. Use the backend analytics to monitor real-time engagement. If an associate spends four hours in your legal folder but hasn't replied to your emails, you have the operational intelligence required to follow up strategically.
Secure Data Room Reviews: Evaluating Compliance Over Interface
When parsing secure data room reviews in 2026, Series A founders and seasoned operators immediately discard feedback focused purely on interface aesthetics. The consensus among successful fundraisers is that the true test of a platform is its ability to withstand an institutional security audit without causing deal friction.
Based on recent 2026 operator surveys, the highest-rated platforms consistently deliver on three critical compliance metrics:
- Zero-Downtime Reliability: During a compressed 14-day diligence window, a crashed server or a slow upload speed can kill deal momentum. Top-tier providers guarantee 99.99% uptime during peak transaction hours.
- Seamless DRM Execution: Founders highly rate platforms where revoking document access works instantaneously, without requiring the investor or their legal counsel to install proprietary software or complex browser plugins.
- Audit-Ready Exportability: When the round successfully closes, legal teams need a complete, cryptographic archive of every document shared and every action taken. Reviews frequently highlight the necessity of one-click, compliance-ready archiving for future M&A preparation.
Frequently Asked Questions About Secure Data Rooms
What is dynamic watermarking in a data room? Answer: Dynamic watermarking is an automated security feature that overlays a viewer's identifiable information—such as their email address, IP address, and time of access—across every page of a document. This actively deters individuals from leaking or unauthorized forwarding of your sensitive financial and legal information.
Does a secure data room prevent screenshots? Answer: While no software can completely prevent a user from taking a physical photograph of their monitor with a smartphone, a dedicated virtual data room uses dynamic watermarking and strict digital rights management (DRM) to ensure that any leaked image is instantly traceable back to the specific user and IP address that captured it.
Are free trial options safe to use for actual fundraising? Answer: Yes, utilizing a secure data room free trial is a standard operational practice for founders. It allows you to build your folder structures, upload dummy files, and test permission settings before a round officially opens. However, ensure the trial version does not handicap core security features like end-to-end encryption or SOC 2 Type II compliance during your testing phase.
Next Steps: Securing Your Raise and Managing Investor Updates
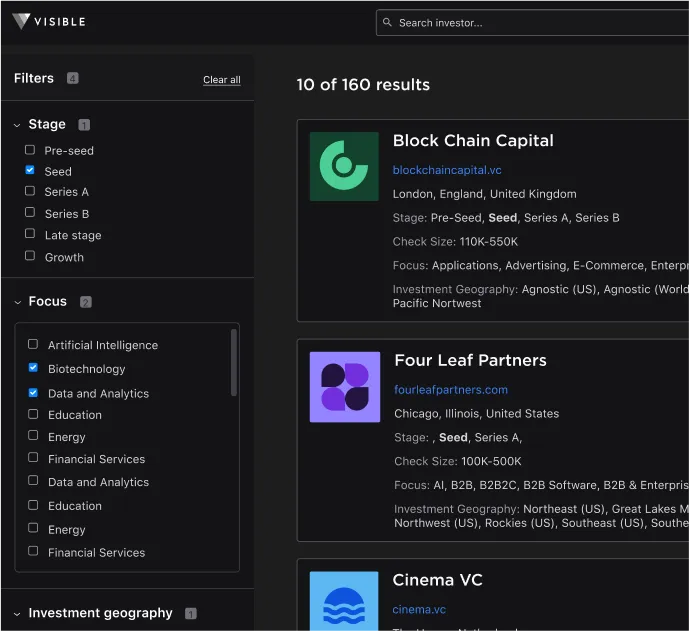
Deploying a secure data room is the critical first step in surviving institutional due diligence. By tightly controlling your intellectual property, enforcing dynamic access rights, and monitoring investor engagement at the document level, you protect your leverage at the negotiation table and accelerate the path to a term sheet.
However, closing the round is not the end of the process; it is the beginning of a multi-year partnership. Once the funds hit your bank account, the focus shifts from defensive document security to proactive relationship management.
Transitioning your new partners out of the diligence phase and into a transparent, consistent reporting cadence is how top founders secure their next round. To maintain that momentum, streamline your post-close communications with investor updates through Visible.vc, ensuring your stakeholders stay aligned, engaged, and ready to support your continued growth.
Frequently Asked Questions
What is a secure data room used for in startup fundraising?
Founders use a secure data room to host and distribute highly sensitive due diligence materials, such as cap tables, pro forma financial models, and IP assignments, to prospective investors. It ensures institutional-grade security, allowing founders to track investor engagement and protect proprietary data during a raise.
Is Google Drive secure enough for venture capital due diligence?
No, consumer-grade cloud storage fails institutional security audits because it lacks Digital Rights Management (DRM) and SOC 2 Type II compliance. Without DRM, a secure data room cannot instantly revoke access to downloaded financial models, leaving your intellectual property exposed if an investor passes on the deal.
What specific documents should I put in my secure data room?
Your secure data room should contain categorized folders for corporate legal documents (articles of incorporation, board minutes), comprehensive financials (three-year historical P&L, pro-forma models), equity details (cap table, option pools), intellectual property assignments, and key HR contracts required for investor due diligence.
What are the most important features of a virtual data room (VDR)?
When evaluating a virtual data room, prioritize dynamic watermarking, document-level analytics, and end-to-end encryption. These features prevent unauthorized screenshotting and forwarding, while analytics give founders critical leverage by revealing exactly which VC partner is reviewing specific financial documents and for how long.